Incident Response services
Incident REsponse
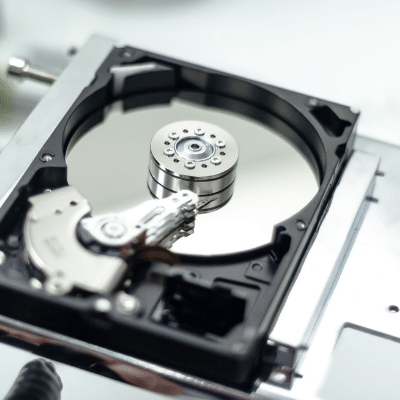
Cybersecurity Incidents aren’t always malicous hackers trying to infiltrate your systems; incidents can range from accidental data exposure to crashed systems. Critical Fault responds to any active incident, helps your organization preserve company data, and works to stop the threat without destroying digital evidence needed for future diagnostics.
incident response Solutions
During every step of the Incident Response process, Critical Fault ensures all evidence is documented and preserved in a way that supports future digital forensic services, if needed.
Identify the threat
Critical Fault’s expert Red Team searches your systems for Indicators of Compromise to identify the threat, assess it’s severity, and develop mitigation strategies. These indicators are documented and preserved as evidence to assist future digital forensics services.
protect data
Poor response to an incident often results in loss of critical company data or data exposures. Additionally, teams can accidentally destroy data while trying to stop the threat. Our security experts ensure as much company data is protected as possible during the event, while mitigating the threat, and during the business recovery process.
stop the threat
Incidents often cause significant down-time to business operations. Once a threat is identified, our security team’s top priority is to mitigate the threat and return your organization back to an operational state as soon as possible. Recommended security strategies are also provided to improve future security controls.
INCIDENT RESPONSE AND DIGITAL FORENSICS
During an incident, the highest priority to an organization is to stop the threat, followed by the need to recover systems to an operational state. In this rush, organizations will often accidentally destroy important evidence needed to perform a root cause analysis. Proper incident response protocols are necessary to ensure evidence is protected.
Digital Forensics typically follows after an organization is operationally restored. Evidence collected during the incident response process is preserved and examined to help determine the root cause of an incident.
Want to learn more? Our Security Experts Are Here For You
Meet Our Red Team
Conoce a Nuestro Equipo Rojo
Kris Wall
CTO, Senior Penetration tester

Jordan Calwell
cSo, Physical security expert
Nick Harris
Penetration tester

Newsletter
Subscribe To Our Newsletter
We've been creating some excellent webinars and local events. Join our mailing list for the latest on industry trends and strategies for cyber defense.
Need Immediate Assistance?
Give us a call (405) 771-6399
Headquarters
3841 E Danforth Rd, Ste 106, Edmond, OK 73034
110 E. Houston St, 7th Floor, San Antonio, TX 78205
Copyright 2024 - Critical Fault, LLC. | Privacy Policy