Why Physical Security Is Cybersecurity
Physical Security Awareness
Physical Security is an important aspect of protecting your organization’s networks, hardware, and data. However, physical security is often overlooked when cybersecurity policies are written, and often times sub-par security measures will be installed, opening the organization to the risk of a malicious intruder.
What Does Physical Security Have To Do With Cybersecurity?
Cyber criminals have been known to breach an organization by infiltrating the physical perimeter and plugging in an infected piece of hardware, or by downloading malicious software directly to systems. These attacks should not be taken lightly, and often indicate a serious risk of insider threats within the organization. Many times, the attacker has performed reconnaissance on the organization and has already mapped out most of the vulnerabilities within the attack surface. Once an attacker has physical access to your networks they can perform several attacks that could be devastating to the organization.
Common Physical Threat Vectors
- An attacker employs Social Engineering to disguise themselves as an employee, maintenance worker, or authoritative figure to gain access to unauthorized areas.
- An attacker plants an infected USB drive into common areas of the organization. The attacker can leave it in a lobby, parking lot, or other organizational watering hole hoping someone will plug in the device. Once plugged in, the device will begin secretly downloading malicious software onto the infected system.
- An attacker deploys his own infected hardware by connecting the device straight into the network. The device is often in an unsuspecting spot and is usually small and unassuming.
- An attacker breaches a server room and installs a device onto the system, allowing the attacker remote access directly to the server.
An attacker targets an internet drop line and intercepts communications, allowing them to collect critical business data. They can also use these drop lines to disrupt services. - An insider threat leverages their privileges and escalates their security credentials to gain unauthorized access to restricted areas.
How Can I Protect My Organization from Physical Security Threats?
-
- Secure your organization’s equipment, paper files, data storage devices, and hardware by limiting physical access to authorized personnel only. Store data, devices, and files in a locked room and keep an active inventory of all information assets being protected. Perform regular inventory checks to ensure there are no unexpected anomalies that could impact your information security, such as missing assets or additional devices.
- Ensure that you are training your employees to practice safe data usage, including:
- remembering to lock doors or cabinets;
- logging out of systems, applications, and networks when away from the computer or not in use;
- never plugging in unfamiliar devices;
- shred documents promptly and regularly when no longer needed;
- how to properly erase data (the “delete” key does not permanently erase data)
- and never leaving sensitive files/devices unattended.
- Implement strong password policies by requiring complex passwords (such as pass-phrases), utilizing multi-factor authentication, and limiting login attempts to unlock devices.
- Ensure all hardware and communications are encrypted at all times.
- Enforce strong Physical Information Security Controls
Physical Information Security Controls
-
- Access Control
- Security Staff
- Proper Lighting Inside and Outside the Building
- Fences
- Doors
- Locks
- Picture IDs
- Video Surveillance
- Intrusion Alarms
- Employee and Management Training
- Equipment Documentation
- Access Control
How Do I Know if My Physical Security Is Protected?
The most effective way to ensure your critical infrastructure is protected is to implement regular physical penetration tests and continue to improve your physical security according to the results of your pen test. Additionally, be certain you are constantly auditing and documenting the physical devices within your organization. If any piece of critical hardware goes missing, or you discover an undocumented device, it could indicate that an attacker may already have gained access to your systems. Keep track of all physical security controls that exist within your organization and consult with your information security team to determine any gaps that may exist in your critical infrastructure.
References
- https://meraki.cisco.com/blog/2021/06/merging-physical-security-and-cybersecurity/#:~:text=Physical%20security%20protects%20cybersecurity%20by,are%20common%20targets%20for%20hackers.
- https://techjury.net/blog/insider-threat-statistics/#gref
- https://www.resolver.com/blog/physical-and-cybersecurity-defense-hybrid-attacks/
- https://www.thinkdsc.com/blog/corporate-physical-security-best-practices
- https://www.cbtnuggets.com/blog/certifications/security/top-7-physical-security-controls
- https://www.ftc.gov/tips-advice/business-center/small-businesses/cybersecurity/physical-security
Related Blog Posts

The Levels of CMMC 2.0 Compliance
Previously, we covered a brief history of the Cybersecurity Model Maturity Certification (CMMC 2.0 Levels) and touched on a few details of what it actually is. For this entry, we will be getting deeper into the internals of CMMC to begin breaking it down into its...

What is CMMC 2.0?
At this point, especially if you ever have contracted or subcontracted with the Federal government, you have probably at least heard the letters CMMC thrown about. There may have even been a twinge of trepidation surrounding the letters. But what do these letters...

Crypto Scams and What to Look For
First, standard disclaimer that this post is opinion and we are not licensed financial professionals, nor is anything meant to be taken as official financial advice. However, we have both direct and indirect experience with cryptocurrency and would like to share our...
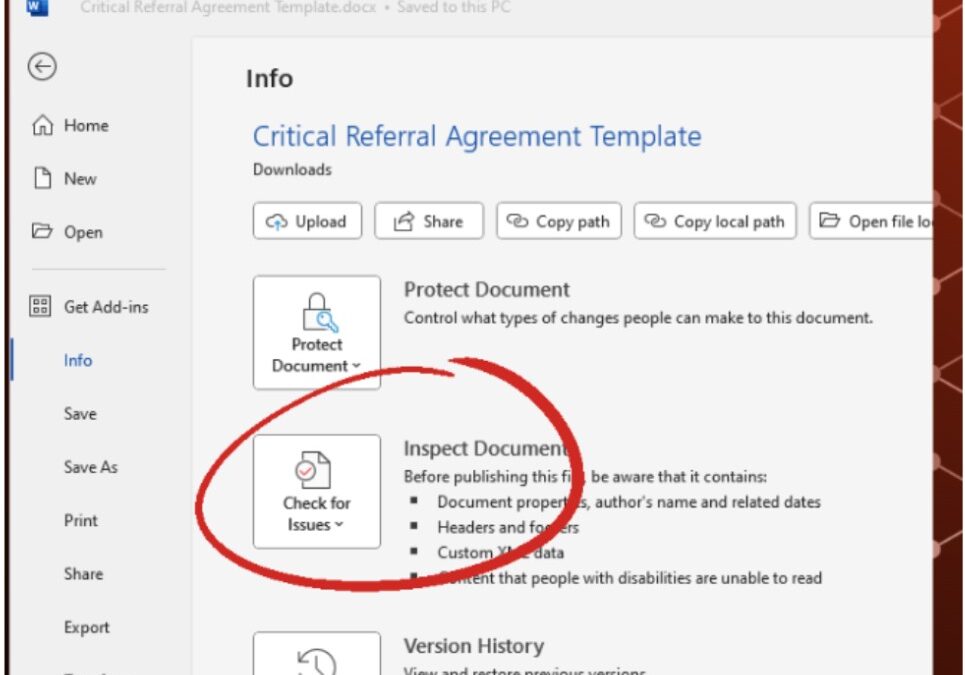
How to Remove Metadata from Word Documents
What is Metadata? According to Britannica: Metadata, data about informational aspects of other data. For example, the date and time of a text message is metadata, but the text of that message is not. The term metadata is a portmanteau of data and meta- (in the word’s...

Newsletter
Subscribe To Our Newsletter
We've been creating some excellent webinars and local events. Join our mailing list for the latest on industry trends and strategies for cyber defense.
Need Immediate Assistance?
Give us a call (405) 771-6399
Headquarters
3841 E Danforth Rd, Ste 106, Edmond, OK 73034
110 E. Houston St, 7th Floor, San Antonio, TX 78205
Copyright 2024 - Critical Fault, LLC. | Privacy Policy



