What Is Penetration Testing and Why Is It Necessary?
What Is Penetration Testing?
Penetration Testing is when an organization hires professional hackers, also known as “ethical hackers”, to identify vulnerabilities in an organization’s security architecture. Penetration Testing takes an offensive security approach: certified security specialists assume the role of the attacker and try to locate and exploit vulnerabilities to gain unauthorized access to an organization’s systems. Once the Penetration Test (pentest) is complete, a detailed report is then delivered to the organization describing any found vulnerabilities, risk ratings, and remediation strategies. The goal of a Penetration Tester, also known as a “pentester”, is to find vulnerabilities and remediate them before a malicious attacker gets the chance. Because the security landscape is constantly changing, Penetration Testers must be stay up-to-date on the newest hacking trends and vulnerabilities. Therefore, it is often recommended to get a pentest annually, if not quarterly, depending on your organization’s security needs.

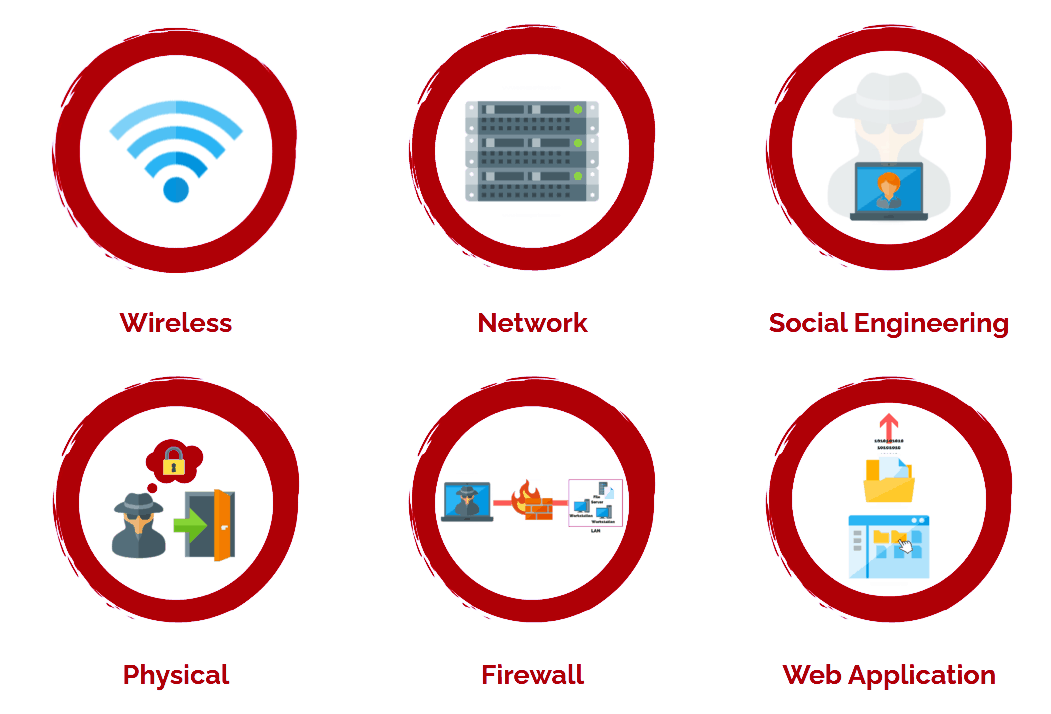
What Are The Different Types of Penetration Testing?
Technically, any system, organization, or structure can be the subject of a penetration test. However, the vast majority of penetration tests fall into three categories.
- Network Penetration Testing
- Physical Penetration Testing
- Application Testing
But as you see below, pentests are often delivered under many different names.
Physical Penetration Testing
A physical security environment is tested by simulating attacks to an organization’s buildings, hardware, and remote devices. Hackers will often deploy malicious hardware into an organization by breaching the building’s perimeter and inserting an infected device into an organization’s network.
Application Testing
An application is tested by employing manual review of source code and software analysis tools, known as DAST and SAST, to identify threats from outside the application and within the source code. Application testing is integral to identifying and eliminating vulnerabilities before production for both web apps and mobile apps.
Penetration Testing Methods
External Testing
External Penetration Testing targets vulnerabilities within an organization’s perimeter systems – typically those directly accessible from the internet. During an External Pentest, the security professional assumes the role of an outside attacker trying to gain unauthorized access to sensitive organizational data. Vulnerabilities are often exploited through web applications, websites, email servers, and social engineering.
Internal Testing
Internal Penetration Testing assumes the role of an insider threat. Insider threats are not always malicious – most of the time vulnerabilities found in this category are accidental. However, should an attacker gain access to these vulnerabilities, they can expose critical organizational data. A Penetration Tester performing an Internal Pentest assumes the role of an attacker who has already gained access to your systems and exploits vulnerabilities within an organization’s internal security architectures.
Why Should My Company Perform Penetration Testing?
Penetration Testing is crucial to identifying vulnerabilities that a standard risk assessment or vulnerability scan can miss. A Penetration Tester introduces the human aspect to information security. 95% of all data breaches are caused by human error. The goal of any Penetration Test is to find out where these errors are occurring and how to remediate them before a malicious attacker. Additionally, many regulatory bodies require regular Penetration Testing to be considered in compliance with security standards.
Regulations and Standards That Influence Penetration Testing
References
- https://www.mitnicksecurity.com/blog/understanding-the-6-main-types-of-penetration-testing
- https://www.imperva.com/learn/application-security/penetration-testing/
- https://www.whitesourcesoftware.com/resources/blog/dast-dynamic-application-security-testing/
- https://www.ftc.gov/tips-advice/business-center/privacy-and-security/gramm-leach-bliley-act
- https://www.ftc.gov/enforcement/rules/rulemaking-regulatory-reform-proceedings/safeguards-rule
- https://www.nqa.com/en-gb/resources/blog/July-2020/guide-to-cmmc
- https://www.pcisecuritystandards.org/documents/Penetration_Testing_Guidance_March_2015.pdf
- https://compliancy-group.com/what-is-hipaa-penetration-testing/
- https://www.breachlock.com/penetration-testing-requirements-for-nist-sp-800-53/
- https://www.cisecurity.org/controls/penetration-testing/
- https://www.imperva.com/learn/data-security/soc-2-compliance/
Related Blog Posts

What to Expect for CMMC 2.0 Assessments
What to Expect for CMMC 2.0 Assessments So now you have put in all the work to meet the requirements of CMMC 2.0 level 1, 2, or 3, but what’s next? Once the rules are finalized and being implemented, companies will need to be able to certify that they are...
CMMC 2.0 Requirements: Level Three
CMMC Requirements: Level Three Now we enter the most nebulous category of CMMC 2.0 requirements: level three. While we know where the requirements will come from, we don’t know exactly how many will be added from the NIST 800-172 publication. While there are...

CMMC 2.0 Level 2 Requirements
CMMC 2.0 Level 2 CMMC 2.0 Level 2-that’s where things really start to get serious. While the controls required aren’t incredibly difficult, there are probably a fair number that most companies haven’t considered before, especially since there are 110 of them. And I am...

CMMC 2.0 Level 1 Requirements
We’re going to start digging through the CMMC levels, starting with CMMC 2.0 Level 1. I will go through the different protection areas and briefly describe what they mean. I don’t intend for this to be a complete guidance, but more an introduction to allow you to be...

Newsletter
Subscribe To Our Newsletter
We've been creating some excellent webinars and local events. Join our mailing list for the latest on industry trends and strategies for cyber defense.
Need Immediate Assistance?
Give us a call (405) 771-6399
Headquarters
3841 E Danforth Rd, Ste 106, Edmond, OK 73034
110 E. Houston St, 7th Floor, San Antonio, TX 78205
Copyright 2024 - Critical Fault, LLC. | Privacy Policy


